Social Engineering - Loose Lips Sink Ships!
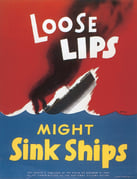 CyberNINES is a veteran-owned small business, our president, Scott Singer, along with several other employees are retired Navy veterans. So, this month we decided our cybersecurity focus would be "Loose Lips Sink Ships!" an old-time navy reference to "beware of unguarded talk". We thought this idiom funnily represents one of the biggest cyber threats today known as Social Engineering.
CyberNINES is a veteran-owned small business, our president, Scott Singer, along with several other employees are retired Navy veterans. So, this month we decided our cybersecurity focus would be "Loose Lips Sink Ships!" an old-time navy reference to "beware of unguarded talk". We thought this idiom funnily represents one of the biggest cyber threats today known as Social Engineering.
What is Social Engineering?
Social engineering is a common technique that hackers use to influence and manipulate people, instead of using real technical hacking skills, to gain access to buildings, systems, or data.
Imagine, instead of a hacker trying to brute force their way into your network and taking over your systems, they simply call or email an unsuspecting employee and try to deceive them into giving up their passwords!
Even if you have the newest state of art firewalls and other security devices protecting your data and critical systems. Companies still have a human workforce that can be easily manipulated by social engineers. Employee training and ongoing programs like phishing simulations can be a great start to keeping employees aware and on alert for this cyber threat.
What to Look out for in a Phishing Attempt!
Suspicious sender’s address.
- The sender's address may imitate a legitimate business. Cybercriminals often use an email address that closely resembles one from a reputable company by altering or omitting a few characters.
Generic greetings and signature.
- Both a generic greeting—such as “Dear Valued Customer” or “Sir/Ma’am”—and a lack of contact information in the signature block are strong indicators of a phishing email. A trusted organization will normally address you by name and provide their contact information.
Spoofed hyperlinks and websites.
- If you hover your cursor over any links in the body of the email, and the links do not match the text that appears when hovering over them, the link may be spoofed. Malicious websites may look identical to a legitimate site, but the URL may use a variation in spelling or a different domain (e.g., .com vs. .net). Additionally, cybercriminals may use a URL shortening service to hide the true destination of the link.
Spelling and layout.
- Poor grammar and sentence structure, misspellings, and inconsistent formatting are other indicators of a possible phishing attempt. Reputable institutions have dedicated personnel that produce, verify, and proofread customer correspondence.
Suspicious attachments.
- An unsolicited email requesting a user download and open an attachment is a common delivery mechanism for malware. A cybercriminal may use a false sense of urgency or importance to help persuade a user to download or open an attachment without examining it first.
How to Avoid Being a Victim?
- Do not provide personal information or information about the company unless you are certain of a person's authority to have the information. Be suspicious of unsolicited phone calls, visits, or emails from someone asking about employees or other sensitive information. If they claim to be from a legitimate organization, try to verify their identity directly with that company, before releasing information.
- If you are unsure whether a request is legitimate, verify it by calling the company directly and ask to speak to the person in the email or voice message. Make sure to verify the company's identity on their website and use that contact information to verify the request. Do not use any information received from a suspicious message/phone call.
- Do not reveal personal or financial information in email, and do not respond to email solicitations for this information. This includes following links sent in email.
- Always check a website's security before sending sensitive information over the internet. Make sure a website is "https://" or has a padlock icon before the URL
- Make sure your devices have anti-virus software and ensure that this is up to date at all times. Firewalls and email filters are effective as well to reduce some malicious traffic.
- Enforce multi-factor authentication (MFA).
What to do if you think you've become a victim?
- Immediately change any passwords, ensure that any duplicate passwords across accounts are updated and that password is not used again.
- Report the incident immediately to the appropriate people in your company, including the IT department, so they can be on alert for any suspicious activity
- If your financial accounts were compromised, contact the financial institution and close any accounts that are affected.
- Keep your eye out for any other signs of identity theft (CISA has a good article here Preventing and Responding to Identity Theft)
- Consider reporting the attack to the police and file a report with the Federal Trade Commission.
Sources: CISA | Avoiding Social Engineering and Phishing Attacks
